When it comes to bad digital – ad fraud is probably the most egregious act out there. So we’re going to highlight the eight types of ad fraud all SaaS marketers should be aware of.
How Prevalent is Ad Fraud?
According to one report, ad Fraud hit it’s peak back in 2015 with projected fraud losses hitting $7.1 billion dollars globally. The most high-profile ad fraud case came from Uber in 2017, where they found that a whopping two-thirds of their ad budget – $100 million – was entirely ineffective.
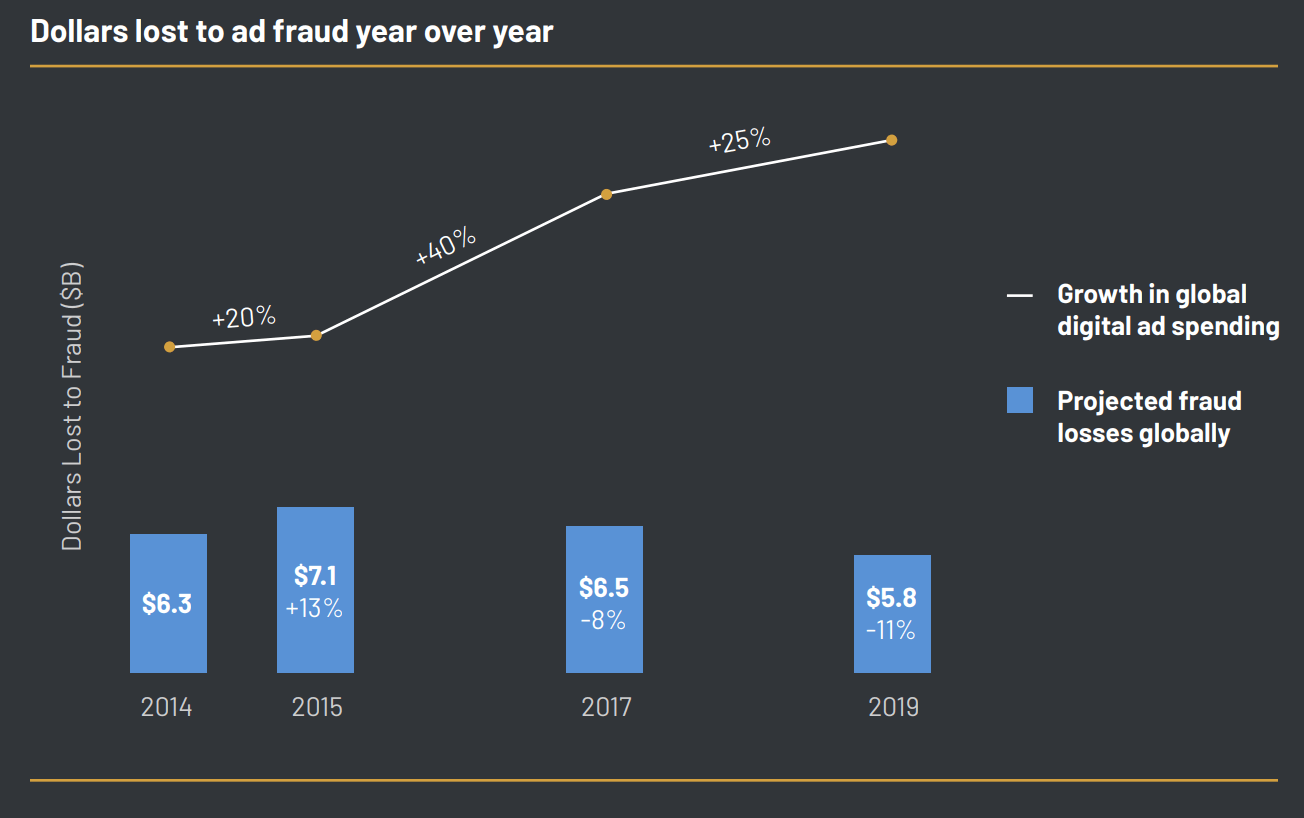
One glimmer of hope is that ad fraud has been declining, even while ad spend has seen significant increases. This trend bodes well for 2021 with COVID keeping a large percentage of people at home and in front of their screens. If you are spending more and more of your advertising dollars on digital channels you should ensure you understand the following types of ad fraud.
8 Types of Ad Fraud All SaaS Marketers Should Be Aware Of
The thing about fraud is that it’s difficult to understand if you’re being deceived and fraudsters are very sophisticated at what they do. However, you aren’t completely powerless. First you can work with those of us who are leading the revolution against bad digital. Second, make sure you understand the following types of ad fraud and the tips for avoiding them.
Domain spoofing
Domain spoofing is all about tricking companies by making them think they are paying for great inventory, when in fact they aren’t. Here are some of the most common forms of domain spoofing:
- Cross-domain embedding is where you believe your ads are showing up on a quality site with quality visitors – but in actuality the fraudster uses an iframe and puts your ads on a different site that has a lot more traffic – but is very low quality – thus making the ad irrelevant for the user and completely misleading you. This type of domain spoofing is more common with websites that most brands try to stay away from like pornography, hate speech and fake news.
- URL substitution is the lazy fraudster’s domain spoofing tactic. They simply replace the URL – so you think you’re advertising in one place and in fact they’re bidding on space somewhere else.
- Custom browsers are most commonly bot enabled. They visit a random site online, but make the URL appear to be the URL where you’re wanting to place ads. So, in your reporting it looks like your ad was placed correctly – when in fact it appeared on some random website.
- Malware preys on unsuspecting humans – infecting their browser so that the malware can hijack an ad placement and replace it with their own.
The bottom line is that domain spoofing is all about defrauding you – the advertiser.
Cookie stuffing
If you’re reading this, you know what a website browser cookie is. Many of the CCPA and GDPR rules revolve around cookies. For more info on these rules, check out our video on What Digital Marketers Need To Know About CCPA and GDPR Rules.
So, fraudsters hijack cookies and add information that isn’t correct about the visitor. This is very common when it comes to e-commerce and affiliate marketing.
Imagine I visit a website and don’t take any action – but my cookie gets hijacked and now my browser believes I went to ACME affiliate and looked at all these products. If I ever do purchase a product these hijacking cookies take credit for my purchase and get paid out through the affiliate CPA platform.
Cookie stuffing is one way fraudulent publishers get themselves paid by CPA platforms. So, if you’re running affiliate programs, make sure you’re working with a reputable firm.
Click injection
While cookie stuffing is set up to take credit for actual sales when they happen, click injection is about taking credit for producing a click. Click injection is very prevalent in mobile ad fraud – think mobile banners or app downloads. The resulting mis-attribution makes you believe certain campaigns or strategies are driving success, when in fact they are doing the exact opposite.
Because this is most prevalent on mobile, fraudsters will work to get users to download malicious apps cloaked as harmless applications like voice changers or noise makers. These seemingly harmless applications will infect a user’s device and run in the background collecting clicks on invisible ads without the user’s knowledge. The more clicks generated – the more revenue for the fraudster.
These malicious apps can go beyond clicks and even steal credit and collect the rewards for legitimate app downloads by the user.
Click spamming
Click spamming is also focused on producing fake clicks. Instead of injecting code at the last second to steal the credit, click spamming floods the system with low-quality clicks in the hopes that one of those clicks makes it through the system and steals the credit.
It’s akin to those emails from some obscure source abroad asking you to provide your bank account information so they can transfer a bunch of money to you. It is unlikely that someone would fall for this – however, it’s a numbers game. Is this completely shady and unsophisticated? Yes. Well, that’s click spamming for ya.
Click spamming can either be software enabled or done by click farms. If you see a huge amount of traffic coming from an obscure part of the world or page visits followed by a download happening in fractions of a second – then you’re probably dealing with click spamming. Click farms are often located in other countries, which makes their clicks relatively easy to identify.
Pixel stuffing
Pixels are really, really small. They’re so small as a unit that a site visitor can hardly see them. So, fraudsters will take a larger ad and put it into such a small space it becomes virtually undetectable by a human – but the system that gives credit for an impression is sure to see it. Now imagine how many ads you could show if they were displayed in a 1×1 pixel area and how many times this can be repeated on a single page! This is what pixel stuffing is.
Ad stacking
Ad staking is just one more way a fraudster can get credit for more ads on a page without changing the look or feel for the user. Basically the user sees one visible ad, but behind that ad are a stack of other ads that the user can’t see but that the fraudster gets credit for.
Ad injection
In #3 we talked about Click Injection. Well ad injection is identical, but instead of producing clicks the fraudster is slipping ads into a space that belongs to a different ad. They do this through browser extensions and adware plugins or by hijacking a server to slip an ad in. AdCumulus even claims fraudsters can place ads on a website that doesn’t normally show ads. Ad injection allows fraudsters to put ads where they don’t belong.
Geo masking
One piece of demographic data that is central to the success of any campaign is the geo targeting. Most marketers know what region of the world or region of a country their most valuable traffic is coming from.
Of course there are certain markets that command larger investments for the high-quality traffic they can produce. Knowing this, fraudsters make you think you’re investing in these high-demand markets, when in-fact they’re paying for low-quality traffic from regions you may not be at all interested in. This is called geo masking.
Ok, that rounds out our list of the 8 types of ad fraud all SaaS marketers should be aware of. Now let’s turn our attention to avoiding all that ad fraud.
avoiding ad fraud
There is no silver bullet or perfect solution to avoiding ad fraud, however, here is where you should start:
- Know Your Data: the more in-tune you are with your data, the easier it will be for you to identify if some anomaly is occurring that could be inflating things – leading to wasted ad spend.
- Research Your Vendors: Before you start investing make sure you’ve got a solid partner you can trust and that you’ve done sufficient due-diligence on any network where you’re planning to deploy capital.
- Benchmarks & KPIs: Catching bad digital comes down to knowing when something is fishy. Leveraging your knowledge of the brand, your KPIs and benchmarks can help you diagnose if you’re on to something new and great or if you’ve got fraud.
- Verify Publishers Are Using New Industry Standards: Because of the prevalence of ad fraud, the industry has begun adopting certain standards. In the case of domain spoofing and ad injection, the Interactive Advertising Bureau (IAB) has developed ads.txt – a list of authorized ad vendors which publishers can add to their site. It is estimated that about 80% of programmatic video ad publishers have adopted this best practice to-date. More recently we’ve seen the development of app-ads.txt to decrease fraud on mobile. Ad.cert is a new standard that is working to prevent ad injection. Ensure these standards are being used.
- Continuing Education: Because of the economic impact of ad fraud there are solution providers who are trying to detect and react to ad fraud at different stages of the transaction process, identify suspicious domains, IP addresses and Cookies. Check back here for more news on ad fraud and the emerging technology that is being built to combat it.
CONCLUSION
We hope this post about the eight types of ad fraud all SaaS marketers should be aware of has been helpful. If you are suspicious you might be experiencing ad fraud or if you’d like a fresh set of eyes to take a look at your data and tech stack to determine how at risk you are for ad fraud – contact us.